Test security flowcharts Security network diagram model cloud diagrams government computer solution devices conceptdraw access example networks architecture cybersecurity solutions information models examples Network security diagrams
Your Guide to FedRAMP Diagrams | InfusionPoints
Data flow diagram Security api Flow security diagram data network slideshare upcoming
Data flow diagram (dfd) software
Data flow privacyFlow dfd lucidchart logical Data flow diagram vs flowchartMicrosoft graph security api data flow.
Applied sciencesNetwork security flow diagram Architecture cybersecurity enterprise iot cyber security diagram system softwareFlow chart for security system..

Security network diagram architecture firewall example computer diagrams cyber clipart model networks conceptdraw recommended microsoft access examples solution devices infrastructure
Security flow data cyber event logging diagram internet logs important why so together showing concerning events au puttingYour guide to fedramp diagrams Security network diagram control devices diagrams computer networks access solution encryption secure model architecture conceptdraw example cloud software area examplesIot & enterprise cybersecurity.
Enterprise password managerFlow data diagram security level dfd system visit yc examples network Data flow diagram in software engineeringCyber security flow chart.

Flow security chart documentation overview api diagram zendesk app diagrams example itunes amazon
Network security modelData flow diagram data security, png, 1506x1128px, diagram, area Data flow mapping template[diagram] data flow diagram exam system.
Data flow diagram showing how data from various sources flows throughFlow data diagrams process threat modeling diagram vs application dfd cloud engineering user owasp source response choose board Access control system flow chartThe following data flow diagram template highlights data flows in a.

Data flow diagram of smart security framework
Data flow diagramSecurity data flowchart vector royalty Process flow vs. data flow diagrams for threat modelingCyber security isometric flowchart royalty free vector image.
Flow webrtc aware modelingData security flowchart royalty free vector image (pdf) solution-aware data flow diagrams for security threat modelingSecurity flow chart test flowcharts flowchart testing structure diagrams validity proxy professional when.
Create a data flow diagram
5 cornerstones to a successful cybersecurity programPassword manager data database manageengine security server flow diagram pro ssl between products reset pmp specifications remote enterprise transmission occur Security flowchartSecurity event logging, why it is so important – aykira internet solutions.
Network security diagramsExternal security policy Data flow and security overview.

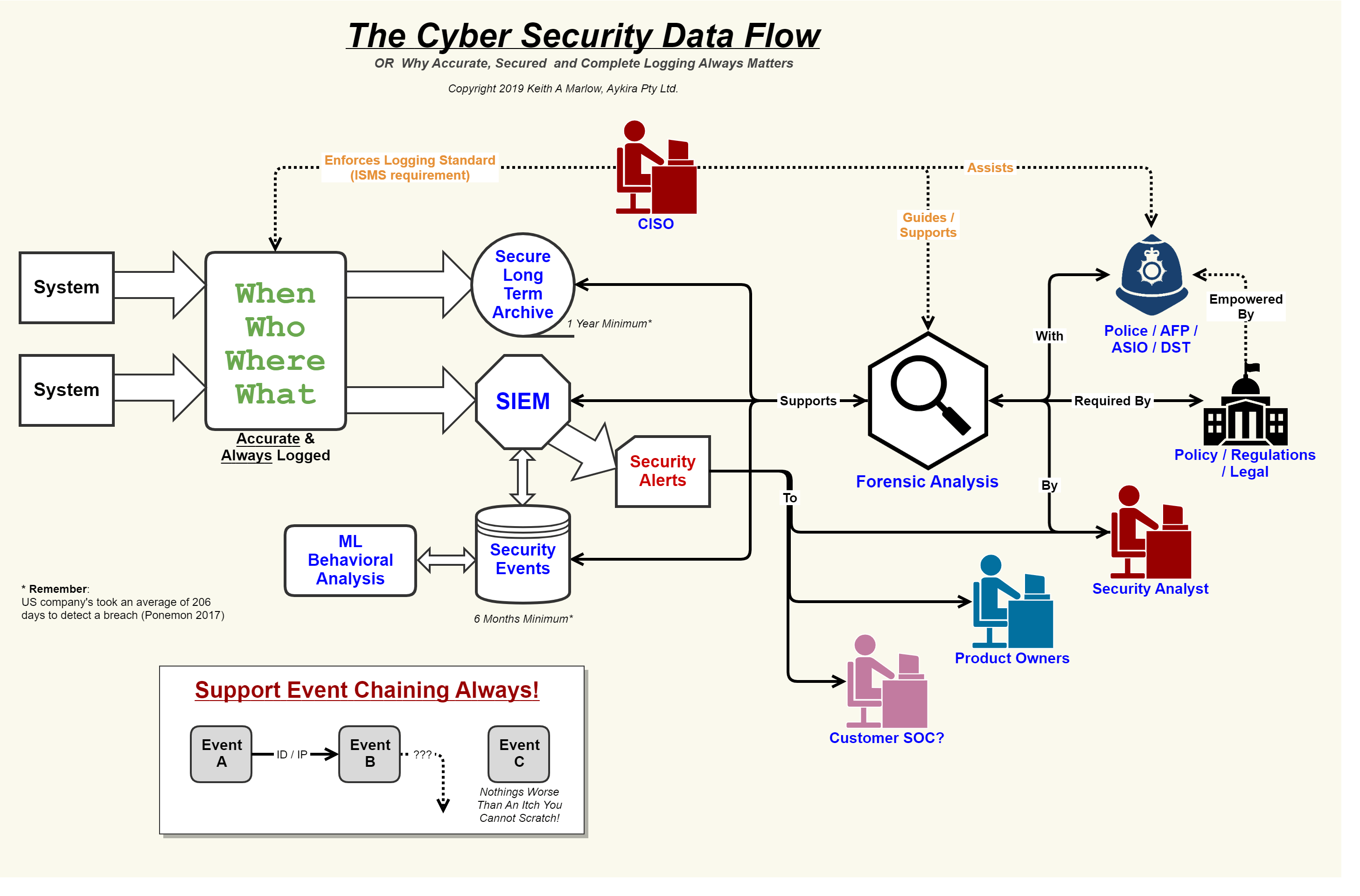
Security Event Logging, why it is so important – Aykira Internet Solutions

Security API - Security Flow Chart and Documentation Overview – Pugpig
Your Guide to FedRAMP Diagrams | InfusionPoints

Network Security Flow Diagram

Data security flowchart Royalty Free Vector Image

Network Security Diagrams | Network Security Architecture Diagram

Network Security Model